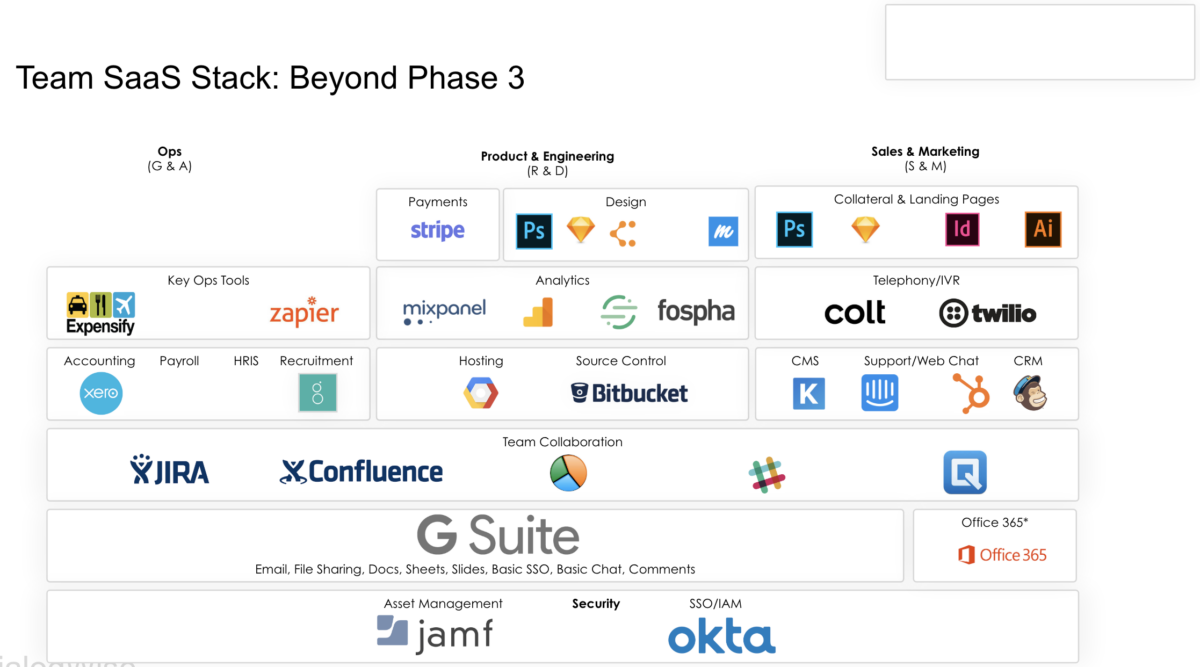
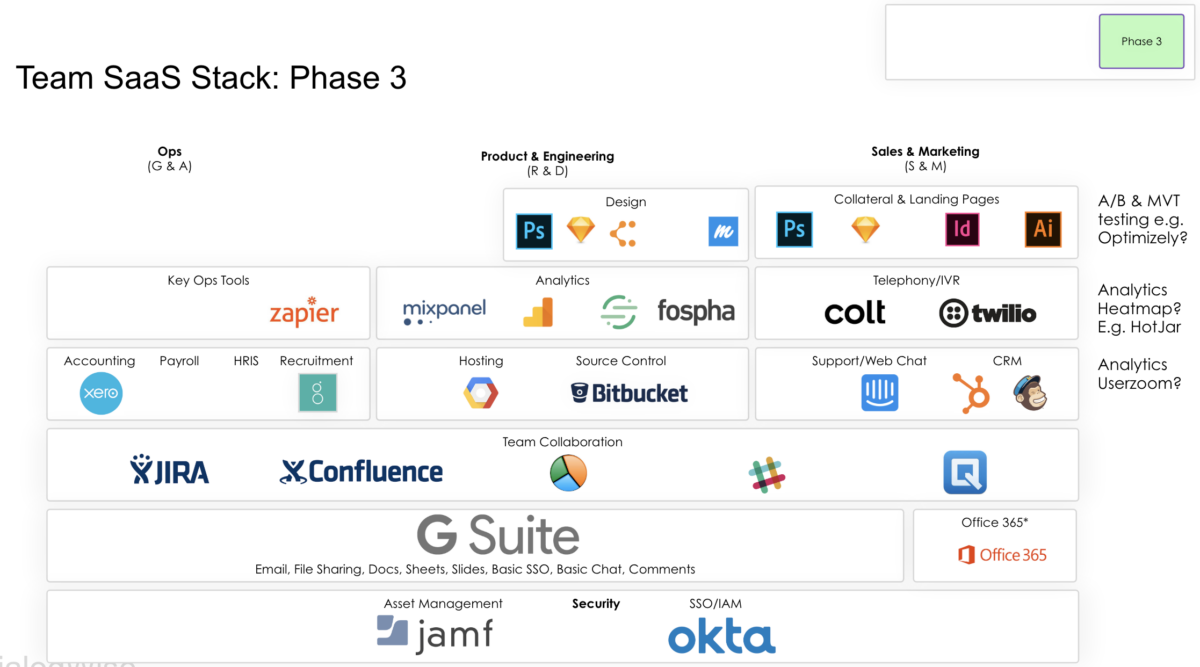
Your business is growing and you are considering expanding your offering to new verticals. The next phase, if you haven’t done it already, is to add payments and ‘quilty-of-life’ tools to help your teams. A good start tech stack for a business which is growing and adding new products is in the diagram. This is the time to also rigorously review your whole tech stack and start taking things out. Carve out 2 weeks every quarter to spend on the tech stack to stay on top of it in terms of cost, usefulness and to ensure you are using tools fit for purpose. Your business has evolved and what worked during the first 6 months might not work now.